North Korean Hackers Again? Cryptocurrency E-commerce Bitrefill Data Breach Suspected to Be Linked to Lazarus
Bitrefill was precisely infiltrated by the Lazarus Group, resulting in the emptying of hot wallets and affecting 18,500 transaction records, bringing North Korean hackers back into the spotlight.
From employee laptops to production secrets: the Lazarus Group’s targeted infiltration
Crypto e-commerce platform Bitrefill announced an official investigation report yesterday (3/17), revealing that the company was subjected to a highly sophisticated cyberattack on March 1. The investigation found that the attack closely resembled tactics used by the North Korea-backed hacker group “Lazarus Group” and its branch Bluenoroff.
In the report, Bitrefill stated that the attack methods, malware characteristics, on-chain fund flows, and reused IP addresses and email addresses all point to this active North Korean organization operating within the crypto industry. The breach originated from an employee’s personal laptop being compromised, from which hackers stole old credentials related to production systems.
Image source: X/@bitrefill Crypto e-commerce platform Bitrefill releases investigation report on the 3/1 cyberattack
Although these credentials were outdated, they became the key to hackers gaining access to Bitrefill’s core systems. By accessing snapshots of production information, the attackers obtained higher privileges and moved laterally within the company’s infrastructure. Subsequently, the hackers targeted some internal databases and specific crypto hot wallets. This pattern of breaching a single endpoint to obtain production secrets is typical of Lazarus Group’s operational strategy, highlighting the severe challenges companies face in managing legacy credentials and endpoint security. Bitrefill emphasized that, although vulnerabilities have been patched and defenses strengthened, the hackers’ professionalism indicates this was a well-planned, targeted operation.
Supply chain anomaly reveals intrusion, hot wallets and gift card stock looted
The attack was first detected through abnormal activity on the business side. Bitrefill’s security team discovered unusual purchasing patterns between the platform and its suppliers. Further investigation confirmed that hackers were exploiting the company’s gift card inventory and supply chain channels for illegal cashing out. Meanwhile, funds from several internal hot wallets began transferring to external addresses controlled by the hackers. In response to this immediate security crisis, Bitrefill quickly took all systems offline worldwide to prevent further damage. Due to the platform’s involvement with thousands of products, multiple payment methods, and cross-border supply chains, the entire security cleanup and system reboot process took over two weeks.
Regarding financial losses, the total amount has not been fully disclosed, but Bitrefill admitted that the hot wallet funds were indeed emptied. During their presence in the system, the hackers conducted multiple targeted queries mainly aimed at asset verification, including cryptocurrency holdings and gift card inventories.
Bitrefill pointed out that the hackers operated with high efficiency, demonstrating an in-depth understanding of the e-commerce platform’s operations. The company subsequently collaborated with multiple professional teams, including zeroShadow, SEAL911 (SEAL Org), and RecoverisTeam, to track the movement of funds on the blockchain and perform digital forensics and cleanup on affected servers.
1.85 million purchase records affected, data breach risk assessment
In addition to financial losses, customer data security has also attracted attention. Bitrefill’s investigation shows that, although the hackers did not fully export the entire database, about 18,500 purchase records were accessed. This leaked information includes customer email addresses, crypto payment addresses, IP addresses, and other metadata. About 1,000 records contain customer names, which are stored encrypted in the database. However, since hackers may have obtained the encryption keys as well, Bitrefill has taken a conservative approach, treating this data as potentially accessed, and has directly notified affected users via email.
Bitrefill emphasizes that the company’s business model minimizes the collection of personally identifiable information (PII), which limits damage in the event of an incident.
Most users are not required to undergo mandatory KYC verification, and when verification is necessary, all documents and information are managed by third-party providers and are not stored on Bitrefill’s internal servers or backups. Based on current log analysis, the hackers’ primary focus was on asset queries rather than the database itself. Nonetheless, affected users should remain vigilant against potential phishing emails or crypto-related scams in the future.
Operations fully restored, Bitrefill commits to absorbing the losses
Currently, Bitrefill’s global operations have returned to normal, including payment functions, inventory replenishment, and account access. The company states that its financial health is sound and profitable in the long term, and will absorb the losses caused by this attack using operational funds. All user account balances remain secure and unaffected. The company’s capital is sufficient to handle this financial impact. To enhance defenses, Bitrefill has implemented stricter internal access controls, automated monitoring systems, and upgraded emergency response procedures and shutdown protocols to ensure faster reaction to abnormal activities in the future, preventing a single endpoint compromise from causing a total system failure.
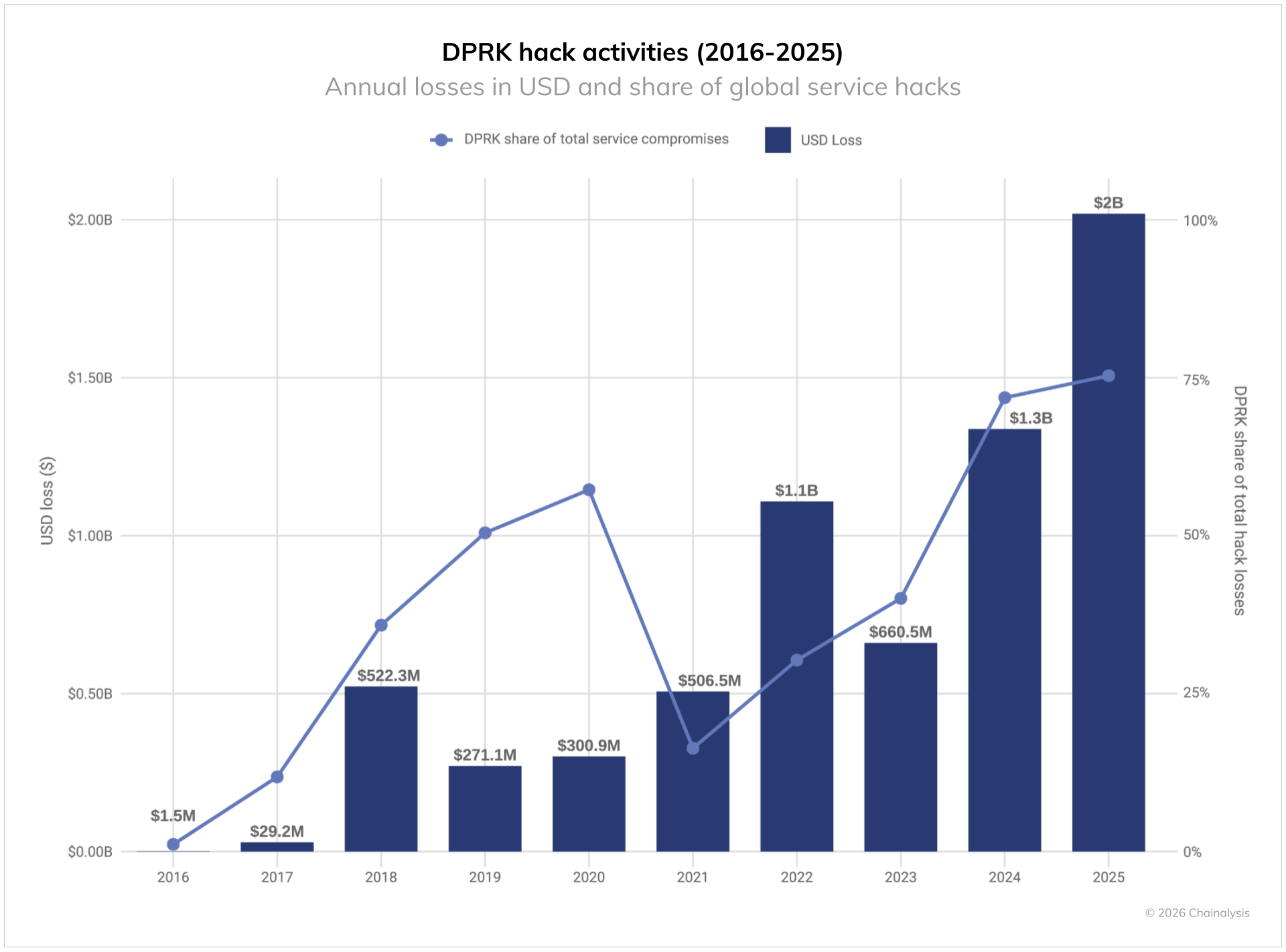
This incident underscores the significant threat North Korean hackers pose to the crypto industry. According to Chainalysis data, North Korea-affiliated groups stole over $2.02 billion in cryptocurrency in 2025, accounting for 59% of total illicit funds that year.
Image source: Chainalysis North Korea-related groups stole over $2.02 billion in cryptocurrency in 2025
This includes Lazarus Group’s historic attack on Bybit early 2025, with up to $1.5 billion stolen, as well as intrusions into Upbit ($320 million) and CoinDCX ($440 million). As North Korea continues to use stolen funds to finance its weapons programs, the nation-state cybersecurity threat to the crypto industry grows more severe. Bitrefill stated it will continue external security audits and penetration tests to maintain resilience against professional hacking organizations.
Further reading
US sanctions North Korean IT scam networks! Illegal proceeds reach $800 million, all funneled into large-scale weapons programs
2025: The darkest year for crypto crime! Hackers stole $6.5 billion, mostly led by North Korea